Everyone’s like, “what are we gonna do about the Russians who hacked SolarWinds?” Here’s a better question: What are we going to do about SolarWinds, whose sloppiness cost the national economy likely tens of millions in damages?
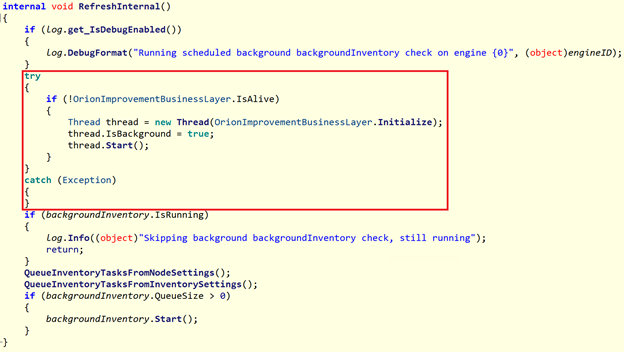
SolarWinds prefers to concentrate on the more complex subsequent hack stages to divert attention from how it all started: the measly 12 lines of the blandest backdoor loader code inserted into the Orion codebase, according to the Microsoft report. 1
The experts are calling this a “supply chain attack,” but was it really? Maybe, at the later stages. But how did these supposed Russians get access to the Orion codebase in the first place? How did they manage to make multiple changes to the code without anyone noticing? Don’t SolarWinds devs use the likes of GitHub to track code revisions? Don’t they have a change control process?
I can almost guarantee you that when full details emerge, the “ground zero” will be some trivial known vulnerability in the SolarWinds corporate network that went unpatched for months or years, allowing the hackers to get a foothold. And the rest of this hack was made possible by SolarWinds’ cavalier attitude toward code change control.
The Microsoft report was interesting in how it consistently overstated the level of sophistication of this attack. Here are more humorous parts:
Indeed they must have been some highly skilled hackers because they did not call their backdoor code a “backdoor.”
“To have some minimal form of obfuscation from prying eyes, the strings in the backdoor are compressed and encoded in Base64…”
Truly mindboggling level of sophistication. Just about every Unix sysadmin out there uses this method to run arbitrarily-complex commands via SSH:
string=$(base64 -w0 script.sh)
ssh -C user@host "echo ${string} | base64 -d | sudo bash"
One of the backdoor initialization checks performed is to make sure it is not running on a test domain using the following regex:
(?i)([^a-z]|^)(test)([^a-z]|$)
I guess every test network in Russia is called “test.” They don’t use .local, .lan, .corp, .example, etc.
Microsoft analysis found it fascinating that each backdoor instance communicates with a unique C2 domain based on the compromised server’s parameters. As opposed to what: hammering the same IP from every backdoor?
It doesn’t take much to impress people these days…
- “Analyzing Solorigate, the compromised DLL file that started a sophisticated cyberattack, and how Microsoft Defender helps protect customers,” Microsoft Security, 19-Dec-2020. [Online]. Available: https://www.microsoft.com/security/blog/2020/12/18/analyzing-solorigate-the-compromised-dll-file-that-started-a-sophisticated-cyberattack-and-how-microsoft-defender-helps-protect/. [Accessed: 22-Dec-2020]